Phishing attacks remain one of the most prevalent and dangerous cyber threats facing organizations today. In this comprehensive guide, we’ll explore how these attacks work and how to protect yourself.
What is Phishing?
Phishing is a type of social engineering attack where cybercriminals attempt to trick individuals into revealing sensitive information such as passwords, credit card numbers, or other personal data.
These attacks typically come through email, but can also occur via:
- SMS (Smishing)
- Voice calls (Vishing)
- Social media messages
- Fake websites
Anatomy of a Phishing Email
Let’s break down the key elements attackers use to make their emails convincing:

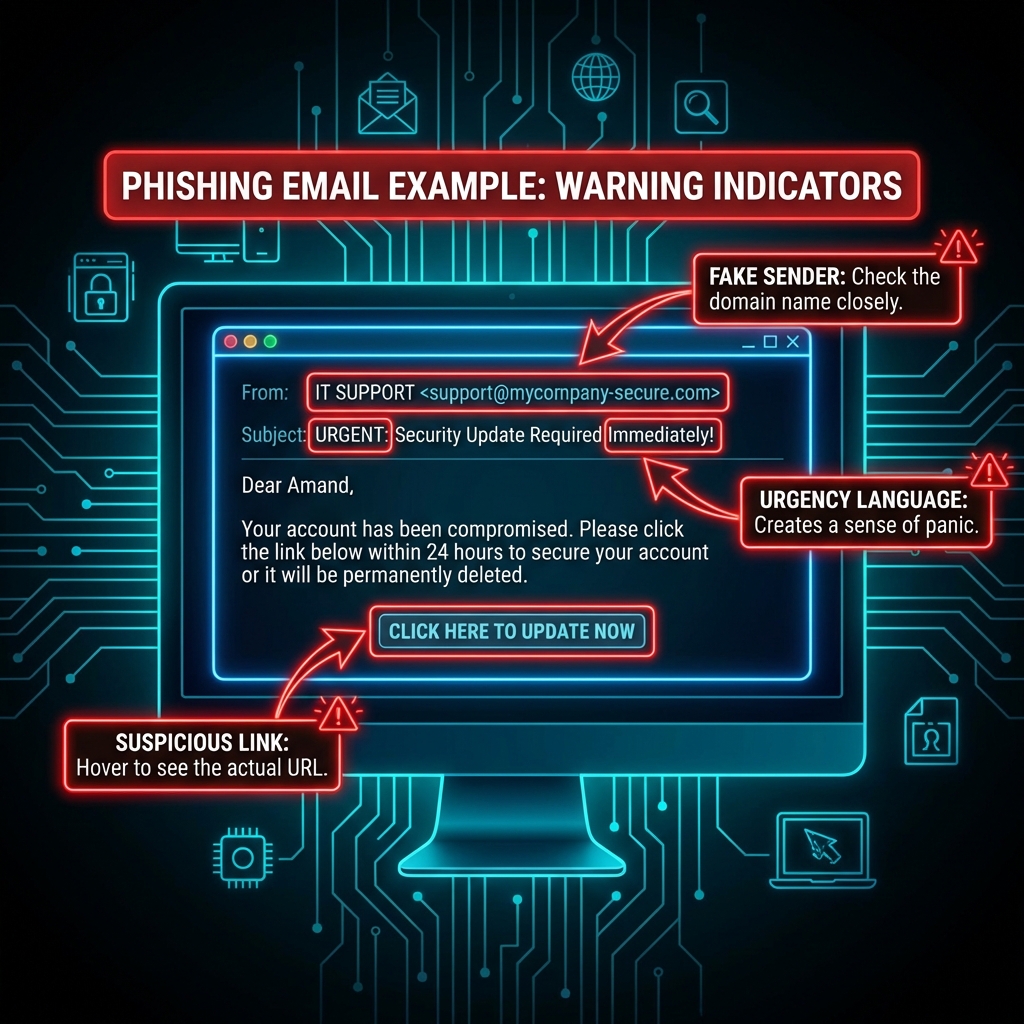
Red Flags to Watch For
- Urgency Language - “Act now!” or “Your account will be suspended”
- Generic Greetings - “Dear Customer” instead of your name
- Suspicious Links - Hover before you click
- Mismatched Domains - Check the actual sender address
- Poor Grammar - Though AI is making this less reliable
Real-Time Threat Detection
Modern security platforms use AI and machine learning to detect phishing attempts in real-time. Here’s what a typical threat dashboard looks like:

Key features of effective threat detection:
- Behavioral Analysis - Identifies unusual patterns
- URL Scanning - Checks links against known threats
- Attachment Sandboxing - Tests files in isolation
- User Reporting - Crowdsourced threat intelligence
Best Practices for Protection
For Individuals
- Enable multi-factor authentication (MFA)
- Use a password manager
- Keep software updated
- Verify requests through alternate channels
For Organizations
- Implement security awareness training
- Deploy email filtering solutions
- Conduct regular phishing simulations
- Establish clear reporting procedures
Conclusion
Phishing attacks continue to evolve, but with the right awareness and tools, you can significantly reduce your risk. Remember: when in doubt, don’t click!
Stay tuned for more security insights from TrustStrike Labs.
